The Healthcare IT Marketplace Opportunity
Healthcare IT spending is undergoing a fundamental transformation as hospitals, health systems, payers, and life sciences organizations accelerate their migration to cloud-based solutions. According to Fortune Business Insights, the global healthcare cloud computing market reached $62 billion in 2025 and is projected to grow to $134 billion by 2030, representing a compound annual growth rate of 16.7%. A significant and growing portion of this spend is flowing through cloud marketplace channels as healthcare organizations seek to leverage existing cloud committed spend for software purchases.
The COVID-19 pandemic permanently shifted healthcare's relationship with cloud technology. Telehealth platforms, remote patient monitoring systems, clinical data analytics tools, and population health management solutions all moved to cloud-native delivery models. As these solutions matured, healthcare organizations consolidated their cloud relationships through enterprise agreements with AWS, Azure, and GCP, creating large pools of committed spend that can be applied to marketplace purchases. For healthcare SaaS vendors, cloud marketplaces now represent a direct pipeline to budget that has already been approved and allocated.
However, healthcare is also one of the most heavily regulated industries in the United States and globally. HIPAA (Health Insurance Portability and Accountability Act) compliance is a non-negotiable requirement for any software that touches protected health information (PHI). Healthcare organizations will not even evaluate a product that cannot demonstrate HIPAA readiness, let alone purchase it through a marketplace. This guide provides healthcare SaaS vendors with a comprehensive roadmap for listing HIPAA-compliant products on cloud marketplaces, navigating compliance requirements, and building a go-to-market strategy that resonates with healthcare buyers.
HIPAA Compliance Requirements for Marketplace Listings
Understanding HIPAA in the Cloud Context
HIPAA establishes national standards for the protection of individually identifiable health information, known as Protected Health Information (PHI). The law applies to Covered Entities (healthcare providers, health plans, healthcare clearinghouses) and their Business Associates (organizations that create, receive, maintain, or transmit PHI on behalf of a Covered Entity). When a healthcare SaaS vendor lists on a cloud marketplace and handles PHI, they act as a Business Associate and must comply with HIPAA's Security Rule, Privacy Rule, and Breach Notification Rule.
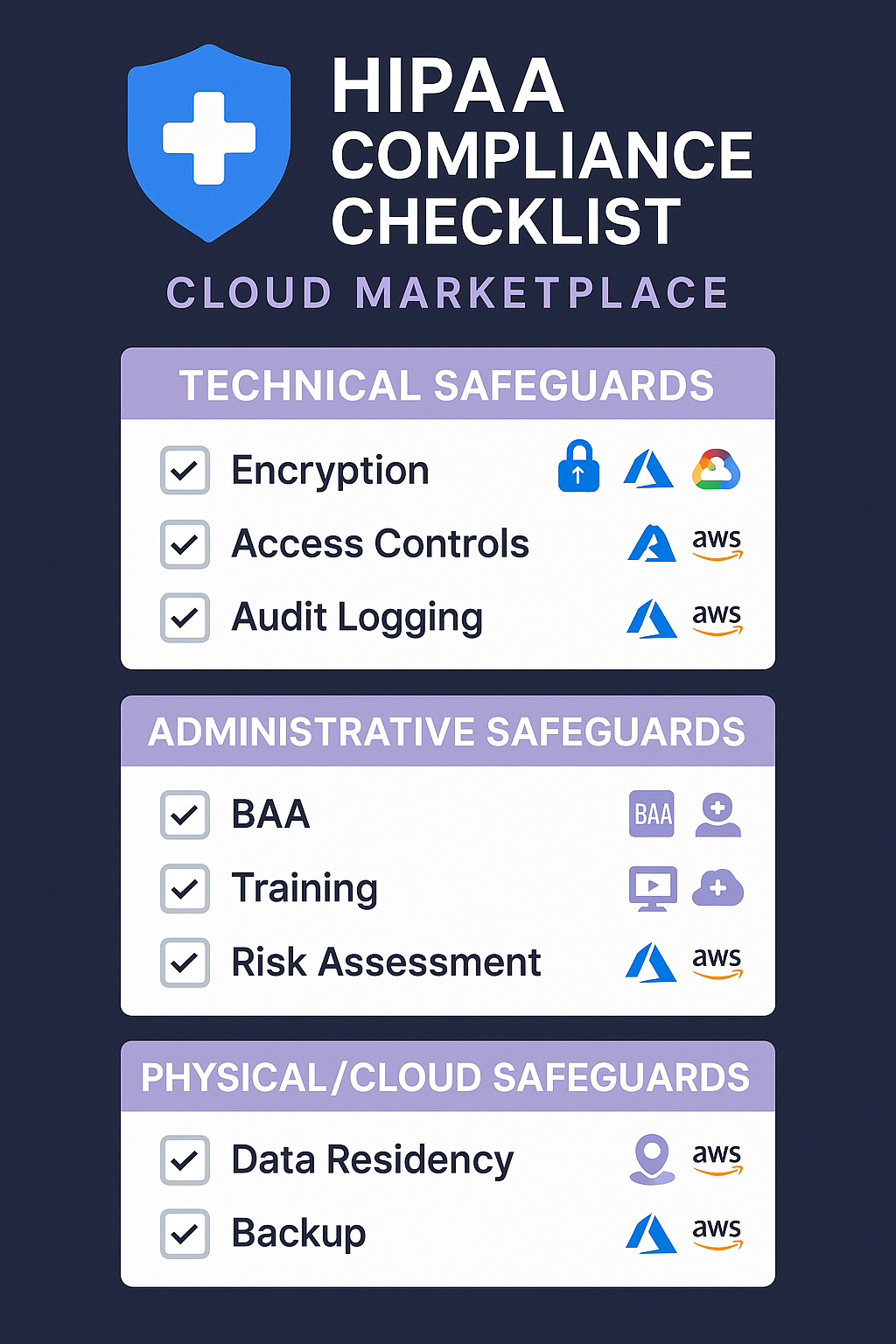
The Security Rule requires administrative, physical, and technical safeguards to ensure the confidentiality, integrity, and availability of electronic PHI (ePHI). For cloud applications, this means encryption at rest and in transit (AES-256 minimum), role-based access controls with multi-factor authentication, audit logging of all PHI access, automatic session timeouts, and data backup and disaster recovery procedures. These controls must be implemented in your application layer, not just the underlying cloud infrastructure.
The Privacy Rule governs PHI use and disclosure, requiring minimum necessary access principles. The Breach Notification Rule requires notification to affected individuals, the covered entity, and HHS within 60 days of discovering a breach affecting 500 or more individuals. Healthcare SaaS vendors must build breach detection capabilities into their products and establish compliant incident response procedures.
Technical Safeguards Checklist
- Encryption at rest: All ePHI must be encrypted using AES-256 or equivalent. This includes database storage, file systems, backups, and any temporary storage. Use cloud-native encryption services such as AWS KMS, Azure Key Vault, or Google Cloud KMS for key management.
- Encryption in transit: All data transmission must use TLS 1.2 or higher. This applies to API communications, web interfaces, data imports and exports, and internal service-to-service communication within the application architecture.
- Access controls: Implement role-based access control (RBAC) with the principle of least privilege. Require multi-factor authentication for all administrative access and for any user accessing ePHI. Support integration with enterprise identity providers through SAML 2.0 or OIDC.
- Audit logging: Log all access to ePHI including who accessed it, when, what they accessed, and what action they performed (view, create, modify, delete). Logs must be tamper-evident, retained for a minimum of six years, and available for review by the covered entity upon request.
- Automatic session management: Implement automatic session timeouts after a configurable period of inactivity (typically 15 to 30 minutes for healthcare applications). Provide session lockout after failed authentication attempts.
- Data integrity controls: Implement mechanisms to protect ePHI from improper alteration or destruction, including checksums, version history, and data validation rules.
- Emergency access procedures: Provide documented procedures for accessing ePHI during emergencies, including break-glass access controls with enhanced audit logging.
Business Associate Agreements on Cloud Marketplaces
A Business Associate Agreement (BAA) is a legally required contract between a Covered Entity and a Business Associate that establishes permitted uses and disclosures of PHI, requires appropriate safeguards, and defines breach notification obligations. Without a BAA, a healthcare organization cannot legally share PHI with a SaaS vendor. For marketplace listings, the BAA landscape involves multiple layers.
First, the cloud provider must have a BAA with the healthcare customer for the underlying infrastructure. Second, the SaaS vendor must have a BAA with each healthcare customer. Third, the vendor needs a BAA with the cloud provider for their own infrastructure usage. This creates a chain of BAAs that must be complete before any PHI flows through the system.
On cloud marketplaces, the vendor-customer BAA is typically attached to the private offer as a custom EULA amendment. AWS Marketplace supports custom contract uploads within the private offer workflow, and Azure Marketplace allows custom terms through its standard contract amendment process. Maintaining a pre-approved BAA template that complies with HHS guidance eliminates weeks of legal negotiation and accelerates deal closure.
FedRAMP and HITRUST Considerations
FedRAMP for Government Healthcare
Federal healthcare agencies including the VA, DHA, and CMS require FedRAMP-authorized cloud solutions. FedRAMP provides a standardized approach to security assessment and continuous monitoring for cloud products. If your healthcare SaaS targets federal customers, FedRAMP authorization is effectively mandatory. The process typically takes 12 to 18 months and costs $500,000 to $2 million depending on the impact level.
AWS GovCloud, Azure Government, and Google Cloud for Government provide FedRAMP-authorized infrastructure, but your SaaS application must also be independently authorized. Most healthcare SaaS vendors pursue FedRAMP Moderate, which covers systems processing PHI. Listing a FedRAMP-authorized product on a marketplace's government section significantly expands your addressable market.
HITRUST CSF Certification
HITRUST CSF (Common Security Framework) is widely recognized as the gold standard for healthcare information security, incorporating requirements from HIPAA, NIST, ISO 27001, and PCI DSS into a single certifiable standard. While not legally required, over 80% of US hospitals reference HITRUST CSF in vendor security assessments, making it a de facto requirement for selling to large health systems and payers.
The certification process takes six to nine months with a HITRUST-approved assessor. Once certified, the HITRUST badge provides immediate credibility on marketplace listings and streamlines procurement, as many healthcare organizations accept it in lieu of proprietary security questionnaires.
How AWS, Azure, and GCP Handle Healthcare Workloads
Each major cloud provider approaches healthcare workloads differently, with varying levels of HIPAA-eligible services, compliance certifications, and healthcare-specific capabilities. Healthcare SaaS vendors should understand these differences when deciding which marketplaces to prioritize and how to architect their products for each platform. The following comparison highlights the key distinctions.
| Capability | AWS | Azure | GCP |
|---|---|---|---|
| BAA availability | Standard BAA for eligible services; signed through AWS Artifact | Standard BAA through Online Services Terms; covers all compliant services | BAA available through Google Cloud agreement; covers eligible services |
| HIPAA-eligible services | 140+ services including EC2, S3, RDS, Lambda, SageMaker, HealthLake | 120+ services including VMs, Blob Storage, SQL Database, Azure Health Data Services | 90+ services including Compute Engine, Cloud Storage, BigQuery, Healthcare API |
| Healthcare-specific services | Amazon HealthLake (FHIR), Amazon Comprehend Medical (NLP), Amazon Transcribe Medical | Azure Health Data Services (FHIR, DICOM, MedTech), Azure AI Health Insights, Text Analytics for Health | Cloud Healthcare API (FHIR, HL7v2, DICOM), Medical Imaging Suite, Vertex AI for Healthcare |
| FedRAMP authorization | GovCloud (High), Standard regions (Moderate) | Azure Government (High), Commercial regions (Moderate) | Google Cloud (Moderate), Assured Workloads (High in preview) |
| HITRUST CSF inheritance | HITRUST CSF certified; shared responsibility model allows inheritance of controls | HITRUST CSF certified; supports control inheritance through Azure compliance documentation | HITRUST CSF certification in progress; limited control inheritance currently |
| Healthcare marketplace category | Dedicated healthcare category with subcategories for clinical, operational, and financial | Healthcare category with AppSource integration for healthcare decision-makers | Healthcare and life sciences category with solution-specific subcategories |
| Data residency options | Region-specific with data residency guardrails via AWS Control Tower | Region-specific with Azure Policy and data residency commitments for EU, US | Region-specific with Assured Workloads for data residency enforcement |
Pricing Strategies for Healthcare SaaS
Understanding Healthcare Buying Patterns
Healthcare organizations have distinct purchasing patterns that influence how SaaS vendors should price their marketplace offerings. Budget cycles in healthcare typically run from October to September for government-affiliated organizations and January to December for commercial health systems. Large purchases often cluster in Q4 of the fiscal year as organizations deploy remaining budget. Healthcare procurement teams are notoriously risk-averse, preferring vendors with established track records and transparent pricing over innovative newcomers with opaque pricing models.
Healthcare buyers also evaluate total cost of ownership (TCO) differently than other industries. They factor in implementation costs, training requirements, integration expenses, ongoing compliance verification costs, and the cost of potential data breaches. A SaaS product priced at $200,000 annually might actually cost $350,000 when implementation, training, and compliance verification are included. Healthcare SaaS vendors should present TCO calculations proactively, demonstrating that their marketplace offering reduces total costs compared to on-premises alternatives or competing SaaS products.
Recommended Pricing Models
Per-patient or per-member pricing is the most natural model for clinical and population health applications because it directly aligns with how healthcare organizations think about their operations. A hospital with 50,000 annual patient encounters or a health plan with 500,000 members can immediately understand the cost implications. This model works well on marketplaces as a contract-based subscription with annual pricing tiers. Per-user pricing works well for administrative and operational tools such as EHR workflow automation, revenue cycle management, and care coordination platforms. It is simple, predictable, and maps cleanly to marketplace contract structures.
Usage-based pricing is appropriate for data-intensive healthcare applications such as medical imaging analysis, genomics processing, or claims analytics where workload volumes vary significantly. Marketplace metering APIs support this model, but healthcare buyers generally prefer a hybrid approach with a minimum annual commitment plus usage overage. This provides the predictability that healthcare finance teams require while allowing for growth. Whichever model you choose, ensure that pricing is transparent on your marketplace listing. Healthcare procurement teams will not engage with vendors whose pricing requires a sales call to understand.
Security and Compliance Documentation
What Healthcare Buyers Expect
Healthcare procurement teams require extensive documentation before evaluating functionality. They will ask for your Security Risk Assessment, policies and procedures manual, workforce training records, incident response plan, and most recent SOC 2 Type II audit report covering Security, Availability, and Confidentiality criteria. HITRUST CSF certification reports are also expected if you hold the certification.
Beyond certifications, buyers expect architecture diagrams showing PHI data flows, encryption key management procedures, disaster recovery documentation with tested RTO and RPO values, and third-party penetration test reports. Maintain a compliance documentation package accessible through a secure portal for efficient sharing during procurement.
Creating a Trust Center
Maintain a public-facing Trust Center that includes your HIPAA compliance program summary, certification list with dates, data processing and residency policies, incident response procedures, and compliance team contact information. Link your marketplace listing directly to this Trust Center so procurement teams can begin security evaluation before contacting sales, differentiating you from competitors who gate compliance information behind NDAs.
Step-by-Step Guide to Listing a HIPAA-Compliant Product
Step 1: Achieve Baseline Compliance
Before listing on any cloud marketplace, ensure your product meets HIPAA compliance requirements. Conduct a comprehensive Security Risk Assessment following NIST SP 800-30 guidelines. Implement all required technical safeguards including encryption, access controls, audit logging, and session management. Develop and document your HIPAA policies and procedures. Train your workforce on HIPAA requirements and document the training. Obtain SOC 2 Type II certification at minimum. Consider pursuing HITRUST CSF certification if your target customers include large health systems or payers. This compliance foundation typically takes six to twelve months to establish if starting from scratch.
Step 2: Sign a BAA with Your Cloud Provider
Execute a Business Associate Agreement with the cloud provider(s) where you will host your product. On AWS, this is done through AWS Artifact. On Azure, the BAA is included in the Online Services Terms when you configure HIPAA-eligible services. On GCP, you sign a BAA through the Google Cloud compliance page. Ensure that you only use HIPAA-eligible services within each cloud provider's portfolio. Using a non-eligible service to process or store PHI violates your BAA and creates compliance risk. Document which cloud services your product uses and verify each one against the cloud provider's list of HIPAA-eligible services.
Step 3: Prepare Your Marketplace Listing
Create a marketplace listing that speaks directly to healthcare buyers. Your product description should lead with compliance and security credentials before discussing functionality. Include HIPAA, SOC 2, and HITRUST badges prominently. Describe your data residency and data handling practices. Document supported integration standards including FHIR R4, HL7v2, DICOM, and any healthcare-specific APIs. Specify which cloud regions your product is available in, as healthcare organizations often require US-based data residency. Include a link to your Trust Center for detailed compliance documentation. Set up at least two pricing tiers: a standard tier for smaller organizations and an enterprise tier that includes dedicated support, custom BAA terms, and enhanced SLAs.
Step 4: Create Your BAA Template
Develop a Business Associate Agreement template that complies with HHS requirements and can be attached to marketplace private offers. Your BAA should define the permitted uses and disclosures of PHI, specify the safeguards you will implement, establish breach notification timelines (within 24 to 72 hours of discovery is typical for healthcare SaaS), define subcontractor management requirements, address data return and destruction upon contract termination, and specify liability and indemnification terms. Have your healthcare compliance attorney review the template, and pre-approve it for marketplace transactions so your sales team can attach it to private offers without waiting for legal review on each deal.
Step 5: Implement Marketplace Technical Integration
Integrate your product with the marketplace's technical systems. Implement the SaaS fulfillment API to handle subscription creation, updates, and cancellations. If using metered pricing, implement the metering API to report usage data. Configure the marketplace's customer onboarding flow to include your BAA acceptance step before any PHI access is granted. Implement your customer provisioning workflow to ensure that new marketplace customers are set up in HIPAA-compliant environments with all required technical safeguards enabled by default. Test the entire flow thoroughly, including subscription changes, cancellations, and the BAA acceptance process.
Step 6: Launch and Engage Healthcare Co-Sell Programs
Once your listing is live, register for healthcare-specific co-sell programs with each cloud provider. AWS has the Healthcare Accelerator program within ISV Accelerate. Azure has the Healthcare Solutions Partner designation. GCP has the Healthcare and Life Sciences Partner Program. These programs provide access to cloud provider healthcare sales teams who can introduce your product to hospital and health system decision-makers. Submit co-sell opportunities for active healthcare deals in your pipeline, and create healthcare-specific solution briefs that cloud provider sales teams can use during customer meetings.
Common Pitfalls to Avoid
- Assuming cloud infrastructure compliance equals application compliance. Just because AWS, Azure, or GCP is HIPAA-compliant does not mean your application running on their infrastructure is automatically compliant. Your application must independently meet all HIPAA Security Rule requirements. The cloud provider's compliance only covers the infrastructure layer under the shared responsibility model.
- Neglecting the BAA chain. Every entity that touches PHI needs a BAA. If your application uses a third-party analytics service, email provider, or customer support platform that may access PHI, you need BAAs with each of those subcontractors. Failing to maintain the complete BAA chain creates compliance gaps that sophisticated healthcare buyers will identify during security assessments.
- Underestimating the sales cycle. Healthcare procurement cycles are long, typically six to twelve months for enterprise deals. Even with marketplace procurement advantages, healthcare buyers require extensive compliance verification, security reviews, and often a clinical validation period. Plan your go-to-market timeline accordingly and ensure your marketplace private offers support the extended evaluation periods that healthcare buyers need.
- Overlooking state-level regulations. HIPAA establishes a federal floor for health information privacy, but many states have laws that impose additional requirements. California's CCPA and CMIA, New York's SHIELD Act, and Texas's HB 300 all contain health data provisions that may exceed HIPAA requirements. Healthcare SaaS vendors serving customers in multiple states must understand and comply with the most restrictive applicable regulations.
- Ignoring interoperability requirements. The 21st Century Cures Act and ONC's information blocking rules require healthcare IT systems to support data interoperability. Healthcare buyers increasingly expect FHIR R4 API support, and CMS regulations require certain organizations to make patient data available through standardized APIs. Healthcare SaaS vendors should build FHIR compliance into their products proactively rather than treating it as a future roadmap item.
List Your Healthcare SaaS with Automatum
Bringing a HIPAA-compliant product to cloud marketplaces involves managing compliance documentation, creating marketplace listings with healthcare-specific content, generating private offers with attached BAAs, tracking metering for usage-based pricing, and coordinating co-sell opportunities with cloud provider healthcare teams across multiple marketplaces. Automatum provides a unified platform that simplifies every step of this process. Manage your AWS, Azure, and GCP marketplace listings from a single dashboard. Generate private offers with pre-approved BAA attachments in minutes. Track usage metering and revenue analytics across all marketplace channels. Coordinate healthcare co-sell opportunities with cloud provider partner teams through integrated pipeline management. For healthcare SaaS vendors navigating the complexity of HIPAA-compliant marketplace listings, Automatum eliminates the operational burden so your team can focus on improving patient outcomes. Visit automatum.io to learn how healthcare ISVs are accelerating their cloud marketplace strategy while maintaining rigorous compliance standards.
No spam. Just the latest releases and tips, interesting articles, and exclusive interviews in your inbox every week.











